We last left off our exploration of China’s censorship system at an in-depth analysis of the content-filtering technical behemoth that is the Great Firewall, and an examination of how the Great Firewall and opposing circumvention tools have evolved in tandem. But the Great Firewall isn’t the only play in China’s book — the Chinese government has also begun to develop intimidatingly powerful Internet weapons that can attack websites that run afoul of authorities’ rules. One of the most recent developments in China’s ever-evolving arsenal is the Great Cannon, a selective attack tool distinct from the Great Firewall that hijacks traffic to individual IP addresses and can arbitrarily replace unencrypted content as a man-in-the-middle.
The Great Cannon first emerged on March 16th, 2015 when GreatFire.org, an organization dedicated to resisting China’s censorship, noticed that the Amazon CloudFront services they rented were being targeted by a distributed denial-of-service (DDoS) attack. The attack sent 2.6 billion requests per hour at peak to GreatFire and pushed the organization’s bandwidth costs with Amazon to $30,000 a day. The GreatFire.org service that was targeted provides proxies to bypass the Great Firewall using encrypted connections via Amazon’s CloudFront service. GreatFire.org blamed malicious JavaScript returned by Baidu servers as the source of the attack, though Baidu denied that their servers were compromised.
On March 26, GitHub also came under the same type of DDoS attack, which was carried out likely in the hopes of coercing GitHub to remove sensitive content, including GreatFire-run GitHub repositories that provide anti-censorship technology and links to mirror sites of the Chinese version of the New York Times. This was not the first time Chinese authorities had attempted to block GitHub. Because GitHub is fully encrypted and the Great Firewall can’t distinguish between innocuous and undesirable packets carrying content from the site, the government could not selectively block offending content, and so instead fully blocked GitHub’s entire site in China in 2013. But the site is indispensable for tech companies in China, and the block caused such an outcry from China’s computer engineers that GitHub was unblocked just two days later. In 2015, the government again tried to force the offending content off GitHub using the Great Cannon.
Let’s explore some of the research that explains how the Great Cannon achieved such large-scale attacks.
A Man-in-the-Middle
In contrast with the Great Firewall, the Great Cannon operates as an in-path system capable of not only injecting traffic but also directly suppressing traffic. This allows it to act as a full man-in-the-middle for targeted flows. The Great Cannon doesn’t actively examine all traffic on a link, but rather intercepts traffic to a set of targeted addresses. This is how its in-path system can keep up with huge volumes of traffic — it only has to process a much smaller stream of traffic destined to targeted addresses, and unlike the Great Firewall it only examines individual packets one at a time, avoiding any computational costs of TCP bytestream reassembly. In addition, the Great Cannon only examines the first data packet of a connection when deciding whether to inject a reply. It does so by maintaining a flow cache of connections used to ignore recent connections that have already been examined.
Though the Great Cannon is a distinct tool, it does have significant structural similarities with the Great Firewall, including its load-balanced architecture where packets are routed to censoring nodes based on source IP address. The Great Cannon is also co-located with the Great Firewall across multiple ISPs including China Telecom and China Unicom, a fact that confirms the government’s involvement.
In the attack on GreatFire.org and GitHub, the Great Cannon intercepted traffic sent to Baidu infrastructure servers that host commonly used analytics, social and advertising scripts. If the Great Cannon saw a request for certain JavaScript files on one of these servers, it either passed the request on to Baidu’s servers as normal (about 98% of the time), or it dropped the request before it reached Baidu and instead sent malicious JavaScript back to the requesting user (about 2% of the time, though it spiked to 17.5% of the time during the attack on GreatFire.org). The affected requesting users were individuals outside China browsing websites making use of a Baidu infrastructure server, like a site with ads served by Baidu’s ad network.
The malicious script enlisted the requesting user as an unwitting participant in the DDoS attacks against GreatFire.org and GitHub. The majority of the infected devices were located in Taiwan and Hong Kong, though the remainder were scattered across the globe. During the attack on GitHub, millions of recruited devices attempted to load a random URL from https://github.com/greatfire/ and https://github.com/cn-nytimes/ every two seconds, in an infinite loop. This resulted in the largest DDoS attack in GitHub’s history, and it persisted for five days. The nature of how these DDoS armies are recruited — from real users scattered around the world, rather than from a concentrated network of infected computers — makes it very difficult to distinguish genuine traffic from fake attack traffic. Attack tactics and targets also continued to evolve and change during the DDoS attack, and attackers made it difficult to locate the injection point of the malicious JavaScript by modifying the IP TTL values of injected packets. The observed TTL values varied over a wide range and couldn’t be used as identifiers for malicious packets.

as a participant in the DDoS attacks against GreatFire.org and GitHub.
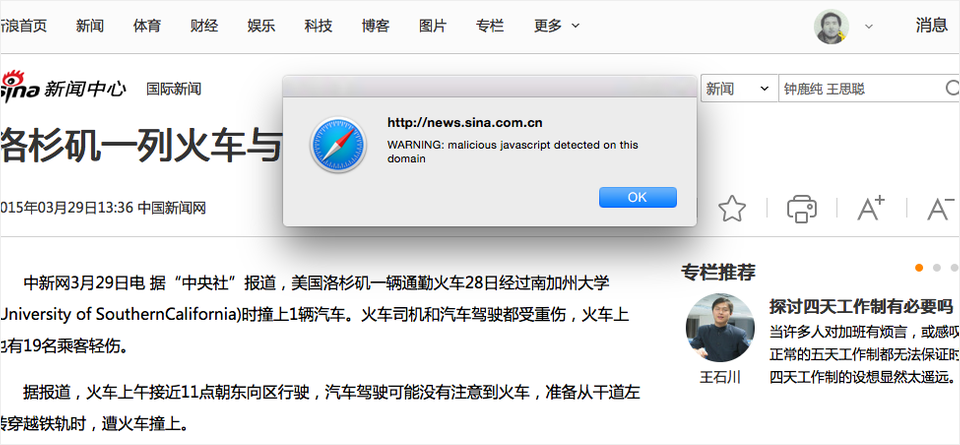
To combat the DDoS attack, GitHub modified the targeted pages to show the following message to users: “WARNING: malicious javascript detected on this domain.” This method warned users that they were unknowingly participating in a DDoS attack, and also prevented the computer from resuming attacks until the user acknowledged the alert. In addition, only users who were exposed to the malicious code would repeatedly see the warning message pop up while browsing other websites.
Implications of Targeted Internet Intervention
The Great Cannon significantly increases the flexibility and power of China’s censorship system. While its design isn’t well-suited for performing traffic censorship (the job of the Great Firewall), it can successfully inject traffic to specifically target unwelcome organizations. The attack on GreatFire.org was exceptionally costly in terms of monetary costs and also disrupted GitHub’s operations. The attack was likely both an attempt to block the operations of an undesirable resource, and also a warning sent to other similar organizations.
Using Baidu traffic in the attack on GreatFire.org suggests that Chinese authorities are willing to pursue domestic stability and security aims at the expense of fostering economic growth in the technology sector. The Great Cannon attacks put Baidu in a difficult position, especially since they directly affected the company’s revenues by interrupting advertising traffic.
The government has a strong agenda, and perhaps what is most striking is that the Great Cannon can also be enhanced in a number of ways. For instance, a simple change in the Great Cannon’s configuration could switch to operating on traffic from a specific IP address rather than to a specific address. This would allow the ability to deliver malware to targeted individuals who communicate with any Chinese server. In other words, if the target ever made a single request to a server inside China not employing encryption, the Great Cannon could deliver a malicious payload to the target. This could happen even if, for instance, the target accessed a non-Chinese website that served ads ultimately sourced from Chinese servers. Encrypted HTTPS connections may not even be enough to safeguard against such attacks, since in practice websites that offer HTTPS protections frequently mix unencrypted traffic from third-party sites into their encrypted traffic. The Great Cannon could still take advantage of this vulnerability by manipulating traffic from one of those third parties.
The introduction of the Great Cannon represents a significant escalation in state-level information control, as it expands China’s efforts beyond censoring websites accessed from within national borders to attacking web services located outside China. Not only that, but the Great Cannon also repurposed the devices of unwitting foreign users for large-scale attacks supporting China’s national priorities. China’s government now has the ability to exploit any foreign computer that communicates with any China-based website not fully protected by HTTPS. It will be fascinating to watch the nation navigate political waters as it attempts to redefine the rules of the Internet, and as its censorship program continues to evolve into a tremendously powerful force that will inevitably affect networks, services and users even outside China’s borders.