The adoption of cloud-based applications has continued as enterprises migrate workloads and services to cloud providers in the quest for agility and scalability. This transformation has, in effect, made the cloud the new data center. Yet, the move to the cloud has not eliminated the need for enterprises to perform identity management tasks for their users.
Traditional tools for identity management, such as LDAP or Active Directory, work for a data center approach but present challenges for cloud-based services. And in this new environment, the stakes could not be higher. Consequences for improperly granting or removing access include hefty fines from regulators for violating rules for HIPAA, GDPR, CCPA, or other industry standards like PCI DSS. Other business impacts include lost productivity and reputational damage.
To properly manage user access in the cloud, there is a lot to do. In fact, if you look at a comprehensive control list like NIST 800-53 Rev 5, you will see 25 controls related to access with 115 sub-controls that cover things from account management and access enforcement to least privilege. So, adding in an external cloud service can sound like a daunting task that will consume more resources and increase risk, but this does not have to be the case.
Challenges with Single User, Multi-Account
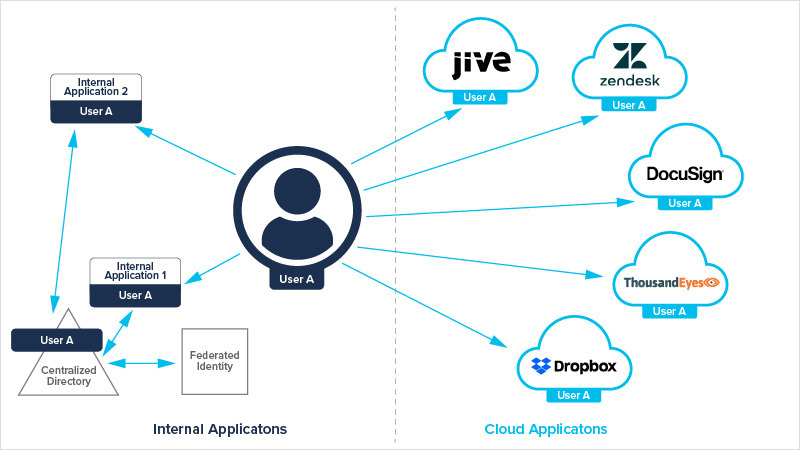
Many users are frustrated with account management because they, too, are trapped in the “single user, multiple account” paradigm, as shown below:
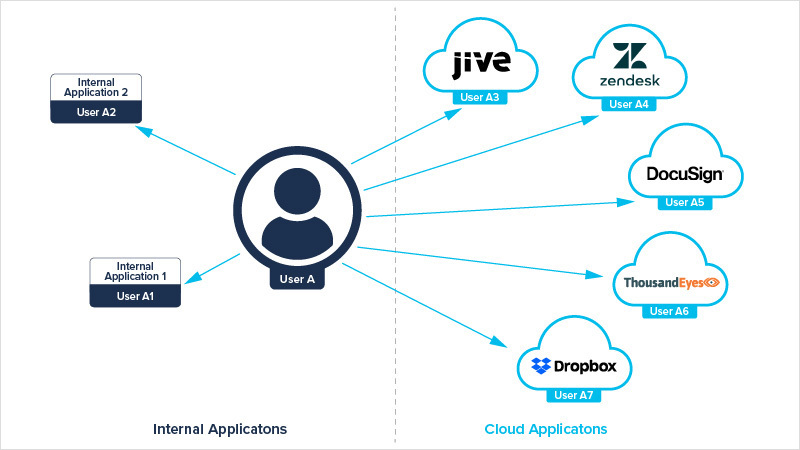
Figure 1 illustrates a user accessing multiple applications with multiple accounts. Each account needs to be managed properly, from creating to deleting it to resetting its passwords securely.
As you might have guessed, there is an alternative paradigm: “Single user, single account,” also known as Identity Federation.
What Is Identity Federation?
You may be wondering what the term Identity Federation means. Fundamentally, it is a way to establish trust between two organizations to authenticate users and convey the information needed to authorize their access to system resources. The best part is that administrators can re-use it to provide this same service between one organization (Organization A) and multiple cloud providers like ThousandEyes, DocuSign, Dropbox, Zendesk, and Jive.
ThousandEyes uses Security Assertion Markup Language (SAML) 2.0, which is an open standard that allows identity providers (like Okta) to pass authorization credentials from an organization to service providers (like ThousandEyes). SAML enables administrators to configure ThousandEyes to use Azure Active Directory, Active Directory Federation Services (ADFS), Google G Suite, Okta, OneLogin, PingOne, miniOrange, and other services to log users into the ThousandEyes console securely.
How Do You Ensure Proper Access?
Great, so now you can authenticate users to a cloud service provider. But how do you ensure they have the correct level of access and permissions? Well, that is where Role-Based Access Control comes into play. You can either use the predefined roles within an application like ThousandEyes, described in the linked article, or create your own.
How Do You Provision and Deprovision Users on an Ongoing Basis?
This is where another protocol comes into play called “System for Cross-domain Identity Management” (SCIM). This protocol can facilitate user provisioning through Azure Active Directory using SCIM 2.0 and 1.1 to compatible identity providers such as Okta.
With these three pieces (SAML for Authentication, RBAC for permissions, and SCIM for provisioning), you can centralize your controls and ensure they are consistently (and in many cases systematically) implemented. Executing on all three helps administrators reduce the risk and complexity of the user management process, all while making life easier for users. Figure 2 demonstrates a user accessing multiple applications with the same account based on federated identity management and a centralized directory.
Doesn’t that look a lot easier? If so, find out if your identity provider and cloud service providers support SAML and SCIM and move toward a more straightforward and secure paradigm.