"Remember, hacking is more than just a crime. It's a survival trait."
This legendary line from the feature film Hackers perfectly encapsulates why organizations like the Open Web Application Security Project (OWASP) release updated category ranking of the top ten vulnerabilities plaguing the world wide web, the latest being for 2021-2022. Allow us to show you how they have changed since last published in 2017 in Figure 1 below.
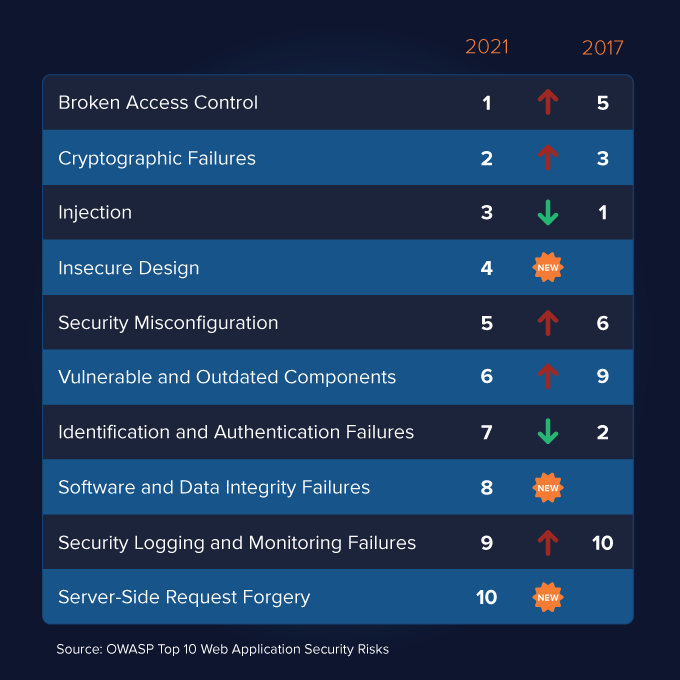
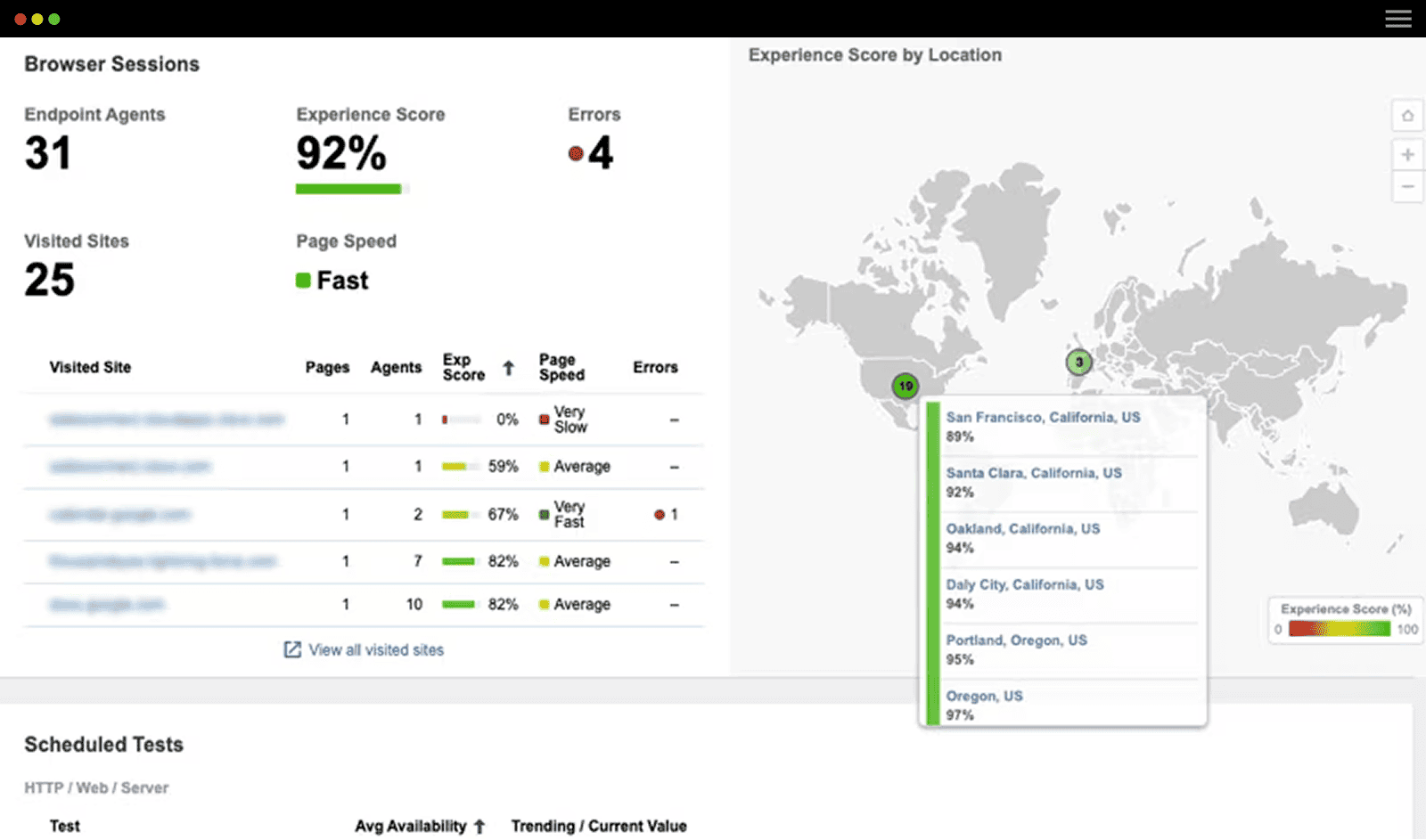
2021 was a challenging year for information security, and 2022 is looking to be similarly so. The good news is that ThousandEyes lives quite safely in the cloud, with the only direct access being through your chosen browser. This setup is, of course, the expectation for a mature SaaS offering these days.
Our web-based entry ramp is the only option where a calculated dose of traffic can reach the platform, making the product portal the only known potential vector for a malevolent actor to fixate on attacking.
Now, considering the vastness of scope implied by the remastered OWASP Top Ten entries, you might ask: How do y’all keep track of all this stuff?
Well, if you’ll allow us a retort with flagrant simplifications:
- Broken Access Control: “Allowing users to do things they shouldn’t be able to.”
- Cryptographic Failures: “Trying to (or forgetting to) do nerdy stuff yourself to protect data.”
- Injection: “Hijacking the browser to make something with higher privileges dance for you.”
- Insecure Design: “Not doing SDLC, overlooking logical separation, avoiding code reviews.”
- Security Misconfiguration: “Not doing hardening, spewing helpful errors, default credentials.”
- Vulnerable Components: “Being blissfully unaware of CVEs and patch management.”
- Identification/Authentication Failures: “Never tried MFA, deploys session management from the late 90s.”
- Software & Data Integrity Failures: “Allowing information to be transformed for fell purposes.”
- Security Logging/Monitoring Failures: “Not gathering enough logs nor safely shipping them”
- Server-Side Request Forgery: “Allowing a service to be commandeered for evil fetches.”
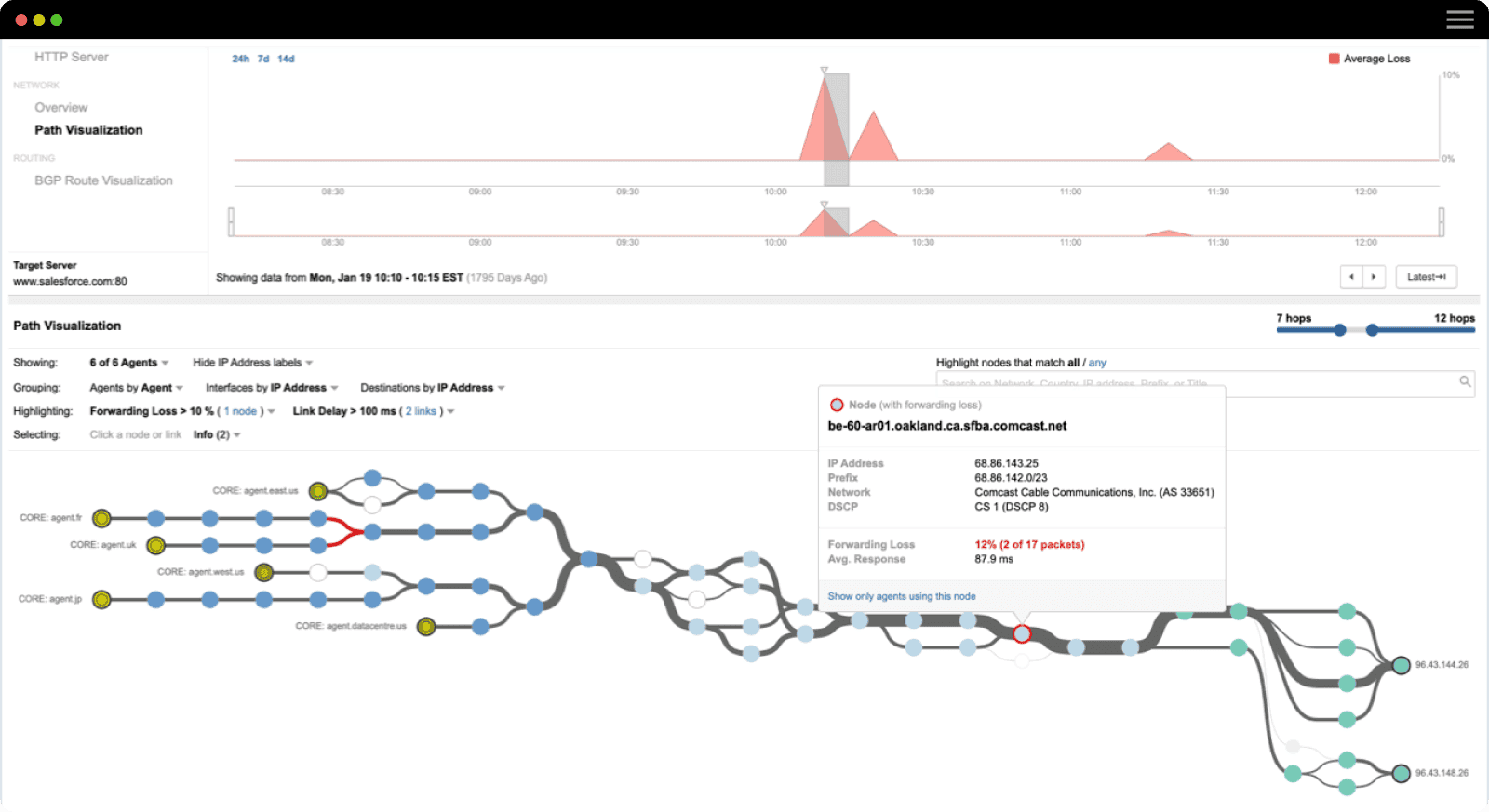
Fortunately, our method for safeguarding against and managing vulnerabilities is quite sophisticated. We incorporate machine-driven analysis in addition to peer reviews of every enhancement written for the ThousandEyes application and any supporting software. Once these releases reach the cloud, we subject them to a rigorous schedule of automated testing, in addition to bi-annual engagements spearheaded internally and by our industry-leading security partners, which include BSI and Bugcrowd.
What’s more, as a part of Cisco, we’re fortunate to be partnered up with some offensively talented folks in the Advanced Security Initiative Group (ASIG)—mind you, they’re hiring—who train their abilities upon our web app at regular intervals. By combining engagements led by ASIG with our own homegrown vulnerability management process, we’re able to field a robust approach for the early detection of bugs in our publicly facing software.
That’s great, but how does your crew respond to zero-days like Log4j?
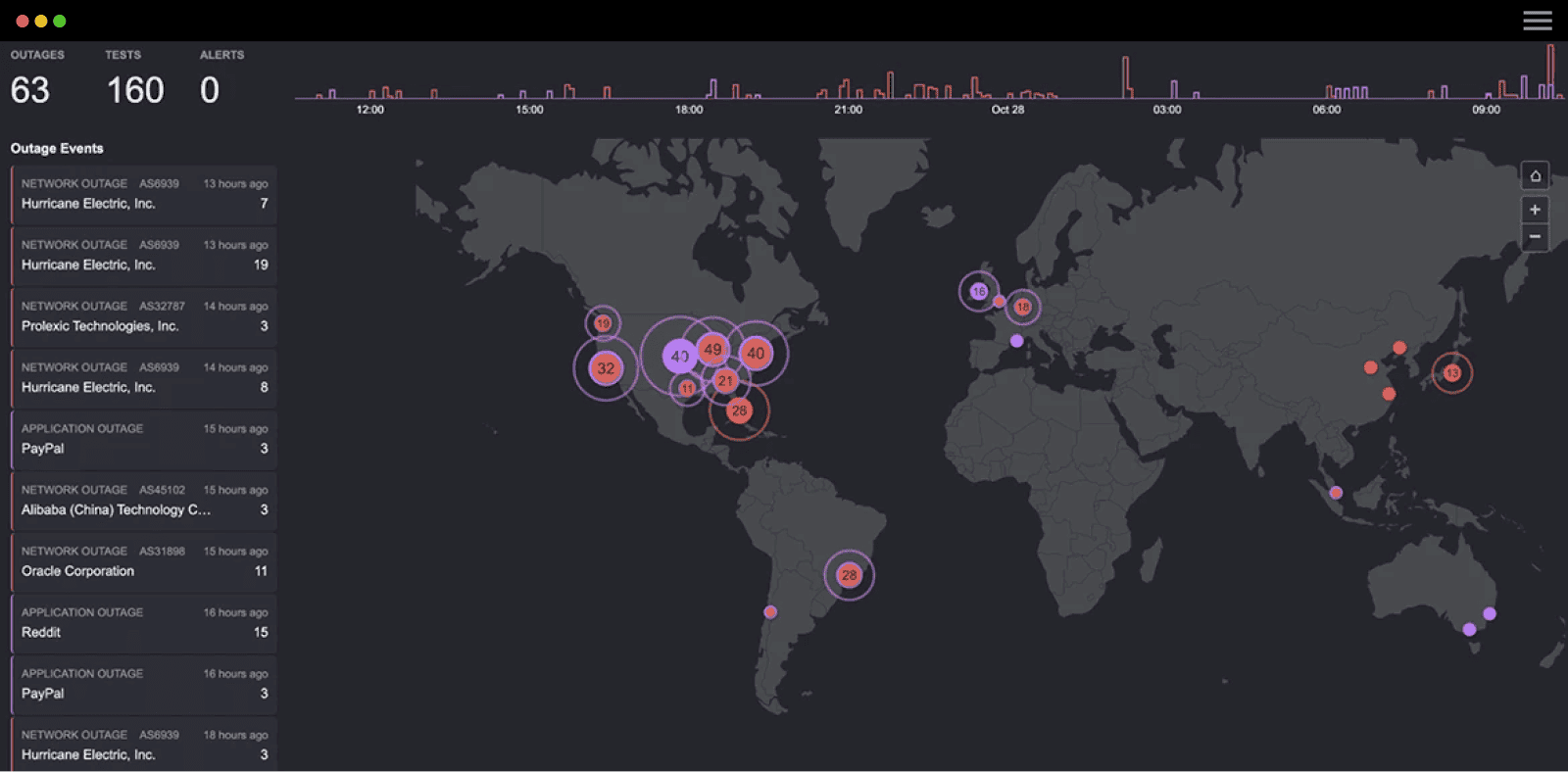
How kind of you to ask–as you might expect, it takes a village. Unfortunately, this past December wasn't exactly paradise for various teams at ThousandEyes. Still, we rallied and were able to swiftly verify that the core CVE did not impact our app. At the same time, we worked behind the scenes to apply mitigations to our supporting infrastructure in the event that the situation continued to unravel. Which, of course, it did.
Log4j/Log4Shell was one of those “thrice in a lifetime” sorts of events. Weekends were destroyed, and entire crops were lost. But in the end, we were really able to come together internally and improve upon our joint response process involving multiple teams during a crisis.
Incidentally, if you’re responsible for anything that lives on the public Internet, and you haven’t yet responded to the threat of Log4j, you’re likely in an egregious violation of OWASP Top Ten #6.
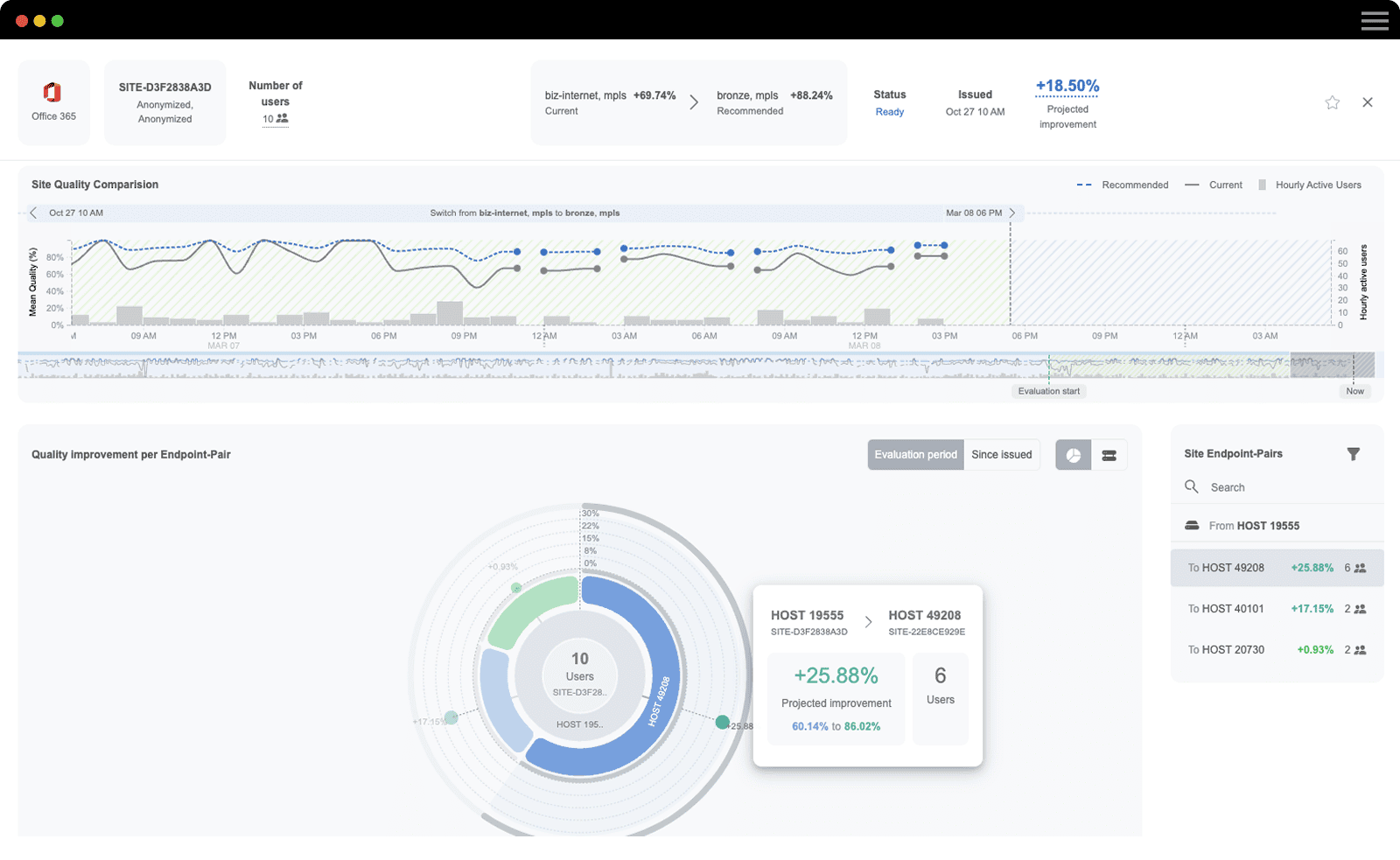
In short, we’re fixated on webserver security here at ThousandEyes. And now that we’re entrenched firmly in the Cisco ecosystem, we expect to continuously improve upon our defense-in-depth strategies, many of which rely upon modern disclosures from legendary foundations like OWASP.