The ThousandEyes platform has become integral to our customers’ network operations. For this reason, we are committed to maintaining their trust and providing transparency in how our platform may impact the privacy of those who use it or provide test data to it.
One way we demonstrate our dedication to privacy and transparency is by routinely evaluating the user information our ThousandEyes web application collects from browsers. We do this because trackers are ubiquitous in today’s Internet, and browsers are the primary tools for accessing our application.
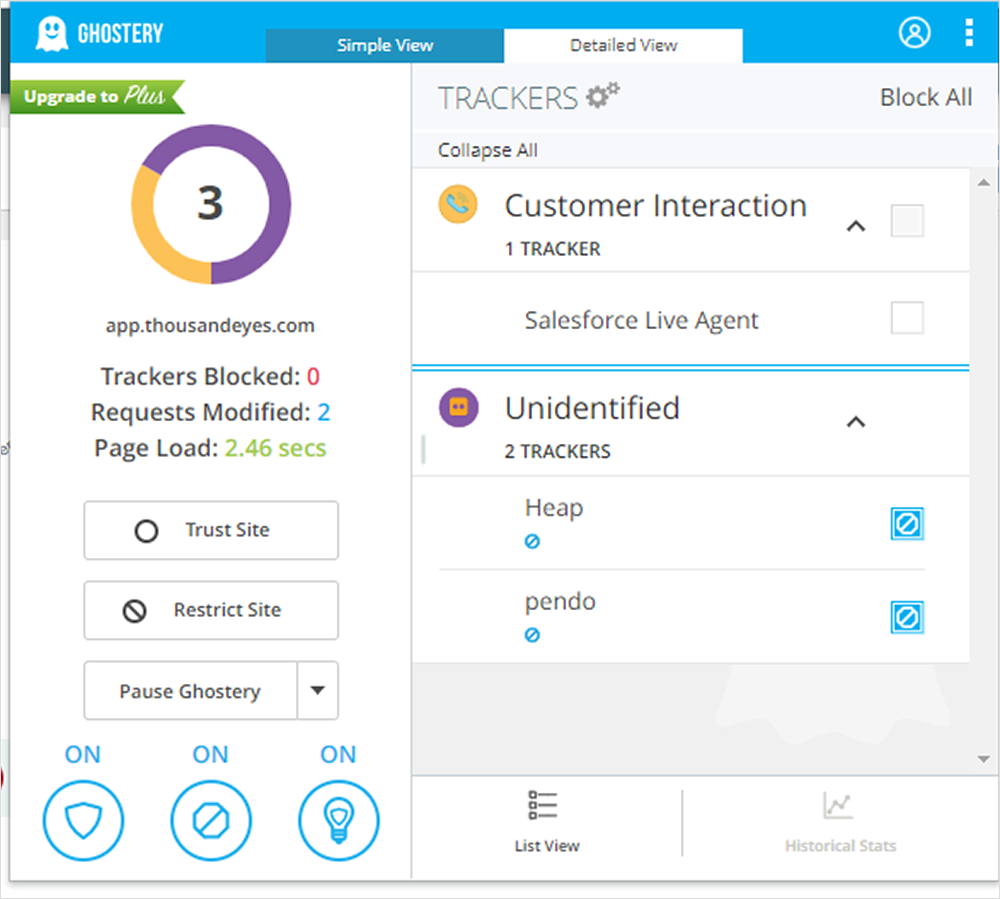
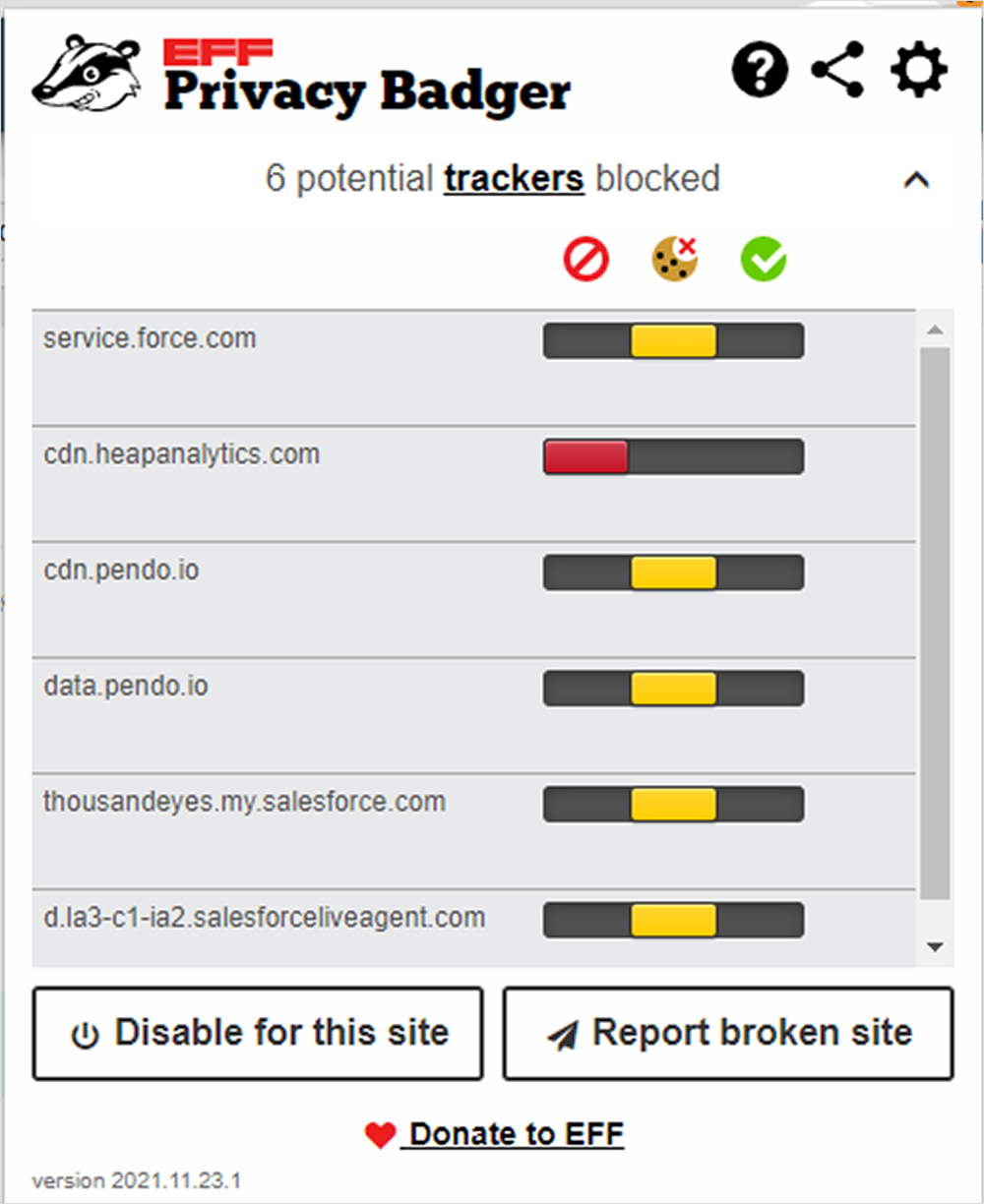
Now, to prevent the tracking of browsing habits, some people rely on tools like Ghostery or Privacy Badger. But as you can see in Figure 1 and Figure 2, their anti-tracking results can vary–even for the same site. Ghostery appears to aggregate some of its results. In comparison, Privacy Badger details the things it notes but leaves it up to the user to determine whether they are related to Salesforce Live Agent, Pendo, or Heap.
As a privacy professional, I like to go a level deeper to better understand what is going on. And in this article, I will show you, too, how I do that.
Cookies ‘n’
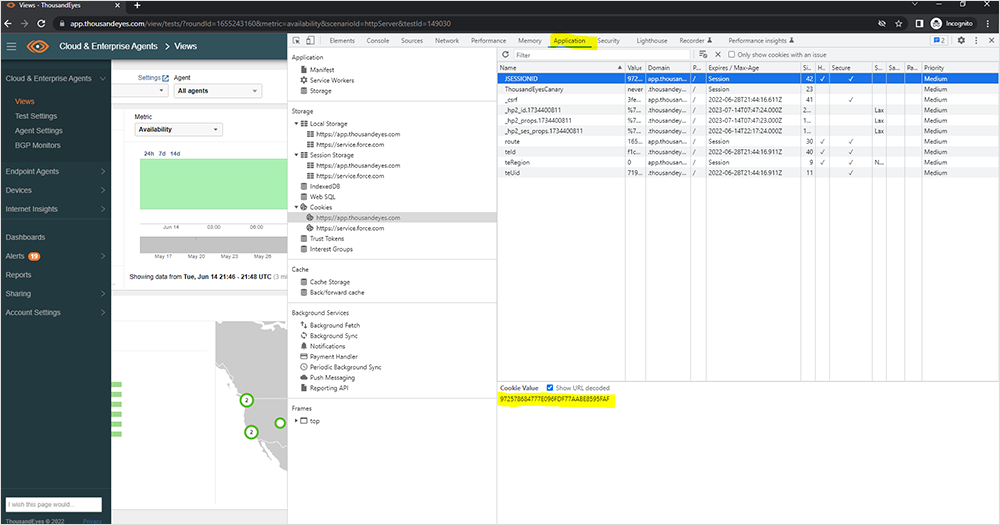
Cookies are one of many ways an application collects information on users. And different trackers can collect information in different ways (as described in this article on trackers and how they work). Therefore, I like to use the Developer Tools built into Chrome when examining a site and the typical places applications store data: Cookies, Session Storage, and Local Storage. Not only will this give me a better understanding of how the application works, but I can also use the details to determine what category a cookie or storage data belongs in (i.e., strictly necessary, functional, video, or marketing tracker). These are nuances that an anti-tracking tool may misclassify.
Cookies are something most of us have been familiar with for years. These text files can facilitate website functionality but may also track your online activity, and thus have privacy implications.
In the example in Figure 3 below, I have logged into the ThousandEyes application in a new Incognito Window, opened the developer tools, and navigated to the “Application” tab. I then expanded the cookies section to see the cookies placed by the ThousandEyes application and Salesforce (which is integrated into the application). Afterward, I selected the JSESSIONID cookie to have the value displayed. There are a lot of other useful things about the cookie fields here that Chrome Devtools nicely describes to help you gain additional context.
About That Storage
Today there are other kinds of tracking technologies that may be used, but they may not be cookies. So, if we look at Local Storage and Session Storage within the browser, we can see what other information the web application has stored about the user.
The main difference between Session Storage and Local Storage is that Session Storage only maintains a storage area while the browser is open (including when the page reloads or restores). Unlike cookies or Session Storage, Local Storage is persistent and continues to store data after the browser is closed.
When we look at the Session Storage used by the ThousandEyes platform (as identified by its URL), we can see Pendo and LiveAgent have been allocated some space for the session.
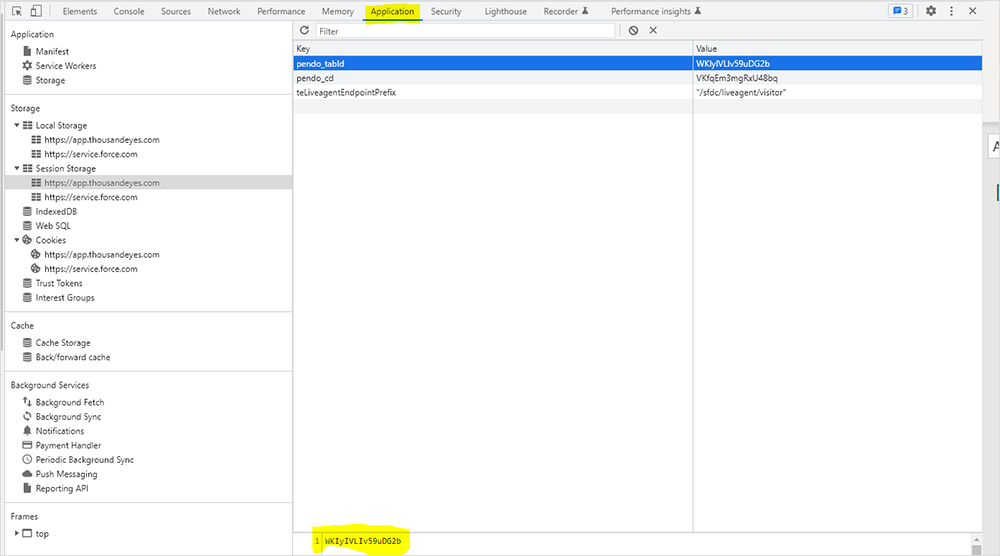
Looking at the Local Storage reveals that “pendo” is also using Local Storage to persist some information. Also, there are a lot of things that seem related to “snapins.”
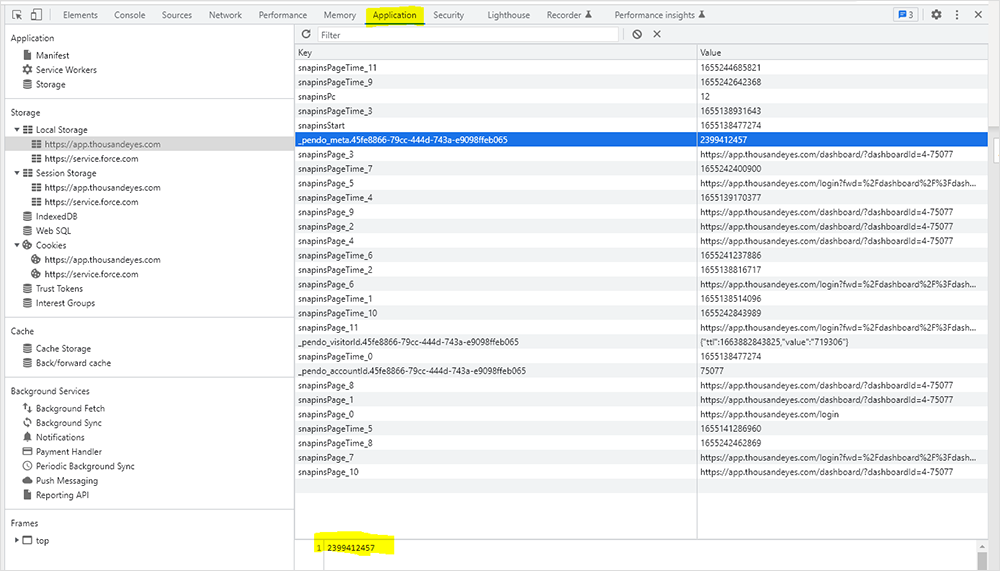
Now that I have all the details about what is being stored in the browser when a user interacts with the ThousandEyes application, I can do some research to find out more about those cookies and the things in Session and Local Storage. Once that’s done, I meet with the team responsible for our application’s web interface. We review the results to confirm my understanding of the things I uncovered in my research and analysis, and I receive answers for any outstanding questions. In doing so, I concluded that the “snapins” stuff was related to the Salesforce Snap Ins chat functionality within the ThousandEyes application and determined the cookies and storage items facilitate the functionality of the ThousandEyes application.
And You Can, Too
I can use the cookie analysis demonstrated in this blog to answer questions internal teams or external customers may have about cookies and storage by the ThousandEyes web application. But before we conclude, I want to leave you with a few tips for checking a web application for cookies and other trackers:
- Use a fresh Incognito Browser window to prevent seeing anything your browser picked up before logging into the web application.
- Go directly to the web application login page in your Incognito tab.
- See what things your tracking blocker(s) stop by managing them as extensions in Chrome and reloading the landing page after login to see what they note.
- Disable any tracking blockers you normally use, and reload the page to get a full picture when you examine the site in Chrome Developer Tools.
- Check different features and functionality like online chat, site documentation, and training videos to see what (if anything) these things add to the browser.
- Copy and paste the information from Chrome Developer Tools into a spreadsheet to help with analysis.
- Save the analysis with the date it was conducted in the file name. Applications change over time, so a date will help you determine the impacts of new features and functionality.