This is The Internet Report, where we analyze outages and trends across the Internet through the lens of ThousandEyes Internet and Cloud Intelligence. I’ll be here every other week, sharing the latest outage numbers and highlighting a few interesting outages.
This week, now that we’re about halfway through 2024, we’re exploring key Internet outage trends we’ve observed this year so far and how IT teams can respond to these evolving challenges. As always, you can read the analysis below or tune in to the podcast where we’ll discuss the 2024 trends further.
Internet Outage Trends
Here at The Internet Report, we’ve been tracking outage data for a number of years. We regularly examine changes in this data every two weeks to keep NetOps teams updated on the latest shifts; however, the long-term trends within the dataset are also incredibly valuable, revealing the evolving challenges faced by engineering teams on the ground and in the operations center.
As we review the 2024 outage data, we see continued evolution, following patterns observed over the past few years. In 2024 so far, the percentage of cloud service provider (CSP) outages has continued increasing—though at a more accelerated rate than seen in recent years. Application outages also remain on an upward trend.
Read on to learn more about these trends and other themes we’re noticing in the Internet ecosystem, or use the links below to jump to the sections that most interest you:
Cloud Incident Trends Accelerate
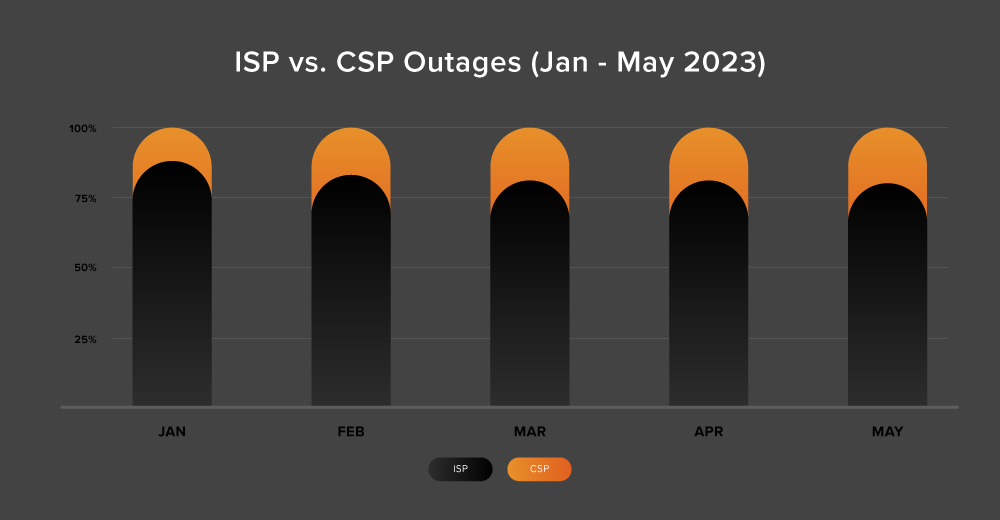
We’ve talked previously about the increase in the percentage of cloud service provider (CSP) outages compared to Internet service provider (ISP) ones. In January, we noted that “the ratio of ISP to CSP outages [had] changed from 89:11 in 2022 to 83:17 in 2023.”
In the first five months of 2024, that ratio rebalance accelerated significantly: to 73:27. Obviously this is not based on a full year of data, but the first part of 2024 was punctuated by some high-profile cloud outages—and the trend line reinforces the need for action. Additionally, when we compare the first five months of 2024 to the five months of 2023, we see a similar upward trend, with the percentage of CSP outages increasing at a greater rate in the H1 2024 period.
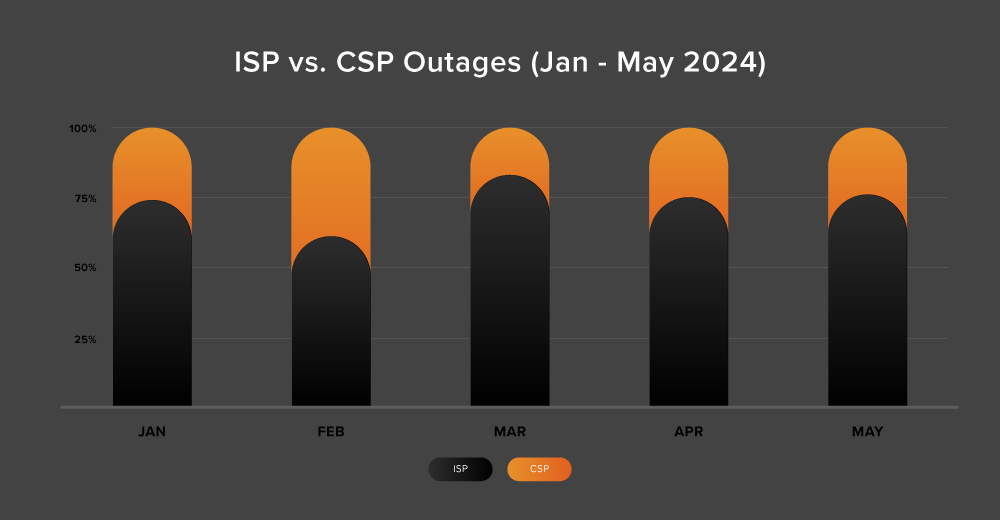
With the prevalence of cloud outages seemingly increasing, along with an increased reliance and use of these environments, ops teams naturally need to understand what this increase in outages means to them—whether an incident is an actual user impacting outage, a scheduled or unscheduled maintenance event, or automated ops or chaos engineering gone wrong on the provider’s end. They need to understand the frequency and duration of these incidents, and—importantly—to what extent they are exposed to the issues.
Given the upward trend in the incident numbers, internal risk tolerances may be tested more frequently this year. Teams will naturally want to understand which cloud ecosystems—or within those ecosystems, regions, and availability zones—are more at risk, and their level of exposure to those. Some re-architecture or redundancy-related decision making or actions may be required, and it’s important that these decisions are based on quality data and actionable insights.
So that’s the first need: With CSP outages increasing, greater end-to-end visibility deep into public cloud environments is required.
Growing Application Outages Call for Broader Insights
Our regular readers, and podcast listeners, will know that application outages often dominate The Internet Report’s fortnightly analyses. This is no accident. The number of application outages continues to grow: We’ve observed an 8% increase in the first five months of 2024, compared to the same period in 2023.
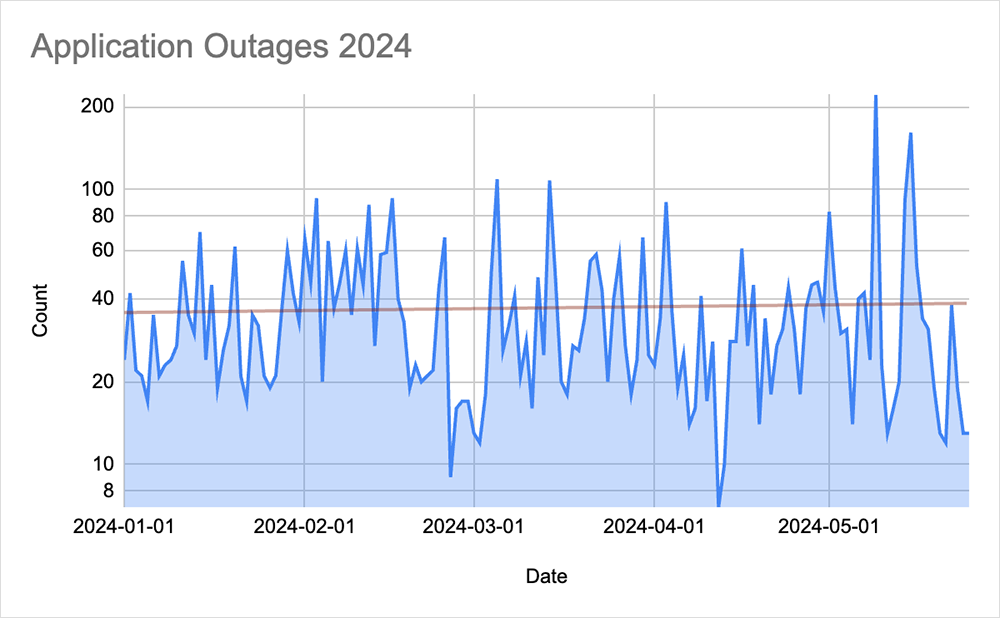
One reason applications deserve attention and focus is that their architecture makes them less resilient to outage conditions than ISPs and CSPs. Internet and cloud providers have been able to improve redundancy and resilience to outages over time; the number of moving parts in an application that sit outside the app developer’s control makes resiliency much more challenging in that space.
Modern distributed applications rely on a mix of in-house and third-party code, cloud services, and APIs. Maintaining visibility across that end-to-end chain for application performance and delivery is already a known need for performance and stability purposes, and will only become more pronounced.
To help assure application resiliency, IT teams require broad visibility and access to contextual, actionable insights across a range of domains—the network, the Internet, the cloud, and more. Having a consolidated view of those insights is equally important so teams can contextualize where performance is beginning to degrade or break in the application architecture.